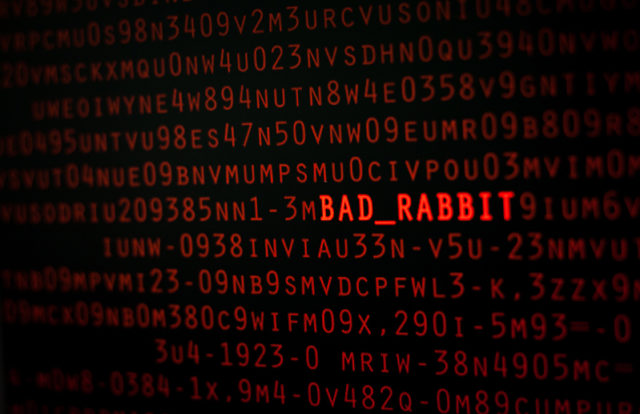
Two days after it was reported that a malware called ‘BadRabbit’ targeted Ukraine, Russia, Japan, Turkey, and Bulgaria, security researchers at Cisco’s Talos unit on October 26 pointed out that NotPetya hackers are likely behind the same attack.
According to a report published in Reuters, Russia-based cyber firm Group-IB said the BadRabbit virus shared a key piece of code with the NotPetya malware that crippled businesses in Ukraine earlier this year. Technical indicators, who analyzed both attacks said there found similarities in the malware coding and hacking methods.
“BadRabbit bore some similarities with NotPetya as they were both based on the same malware, but large parts of code had been rewritten and the new virus distribution method was less sophisticated”, researchers said.
Researchers added that both BadRabbit and NotPetya employed same hacking tool called ‘Eternal Romance’, which is believed to have been developed by the U.S. National Security Agency before being stolen and leaked online in April. However, some experts have cautioned that this might be a trick to mislead investigators about their identity.
The Guardian reported that BadRabbit malware’s code has referred to the names of two dragons from Game of Thrones and the character Grey Worm.
In June 2017, Ukraine’s energy, telecommunications and financial sectors were targeted by a hacking group called ‘Black Energy’. It is suspected that Russia was behind carrying out NotPetya cyber attack, an allegation that it denies.





















