
The Federal Bureau of Investigation (FBI) recently issued a warning for public and private enterprises in the United States about Magecart attacks, also called e-skimming or web skimming attacks, which are carried out by exploiting security flaws in open-source online stores.
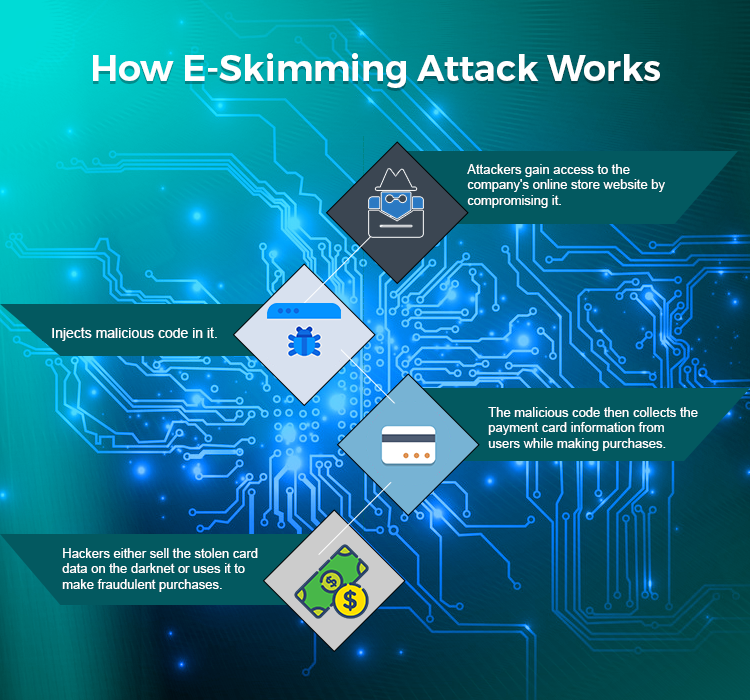
In Magecart attacks, hackers gain access to a company’s online store website by compromising it and hide malicious code in it. The malicious code then collects the payment card information from users while making purchases on the infected site. It’s said that hackers either sell the stolen card data on the darknet or uses it to make fraudulent purchases.
FBI stated that Magecart attacks have been active since 2016, but they’ve increased in 2018 and 2019, and even using diversified attack methodology to launch attacks.
“This warning is specifically targeted to small and medium-sized businesses and government agencies that take credit card payments online. E-skimming occurs when cybercriminals inject malicious code onto a website. The bad actor may have gained access via a phishing attack targeting your employees—or through a vulnerable third-party vendor attached to your company’s server,” the FBI said in a statement.
FBI has suggested security guidelines for businesses to protect themselves from cyber-attacks, which include: Update and patch all systems with the latest security software; Change default login credentials on a regular basis; and Educate employees about safe cyber practices.
In July 2019, the Magecart hacking group was held responsible for a data breach that impacted several websites by injecting malicious code. According to a report from threat intelligence firm RiskIQ, the hackers used a “spray-and-pray” approach to compromise and plant malicious code on over 17,000 domains since April 2019. RiskIQ stated the attackers have been active in web skimming for a long time and started compromising unsecured S3 buckets in early April.
By compromising a few sites, the malicious code spread to thousands of other sites, including Picreel, Alpaca Forms, AppLixir, RYVIU, OmniKick, eGain, and AdMaxim.









